Business Continuity Management (BCM):
Business continuity management is a framework which is used to detect the exposure of organization to internal and external threats. It can include disaster recovery, business recovery, crisis management, incident management, emergency management and contingency planning. In order to build business continuity management plan, one should know the importance of continuity and the preparedness it needs. BCM focuses on overall continuity risks.
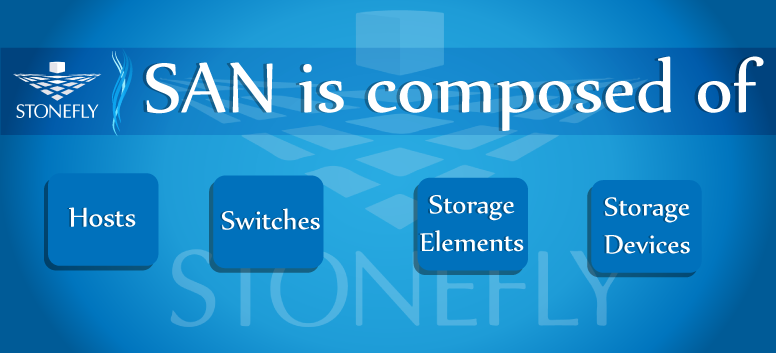
SAN is composed of:
- Switches
- Storage elements.
- Storage devices.
How SAN works?
SAN reorganizes the storage resources of the common user network in an independent, high performance network. Each server can then, access the shared storage. When the host wants to access the storage device in the SAN, the host has to send the block based access request for the respective storage device. Block level storage, raw volumes of storage are created and each block can be controlled as an individual hard drive. These Blocks are controlled by server based operating systems and each block can be individually formatted with the required file system. Block level storage is usually deployed in SAN. This level of storage also offers boot-up of systems connected to them.
Three principle components of SAN:
Storage Area Network is generally accumulated by using three principles:
- HBAs (host bus adapters).
- Switches (attached to the storage arrays)
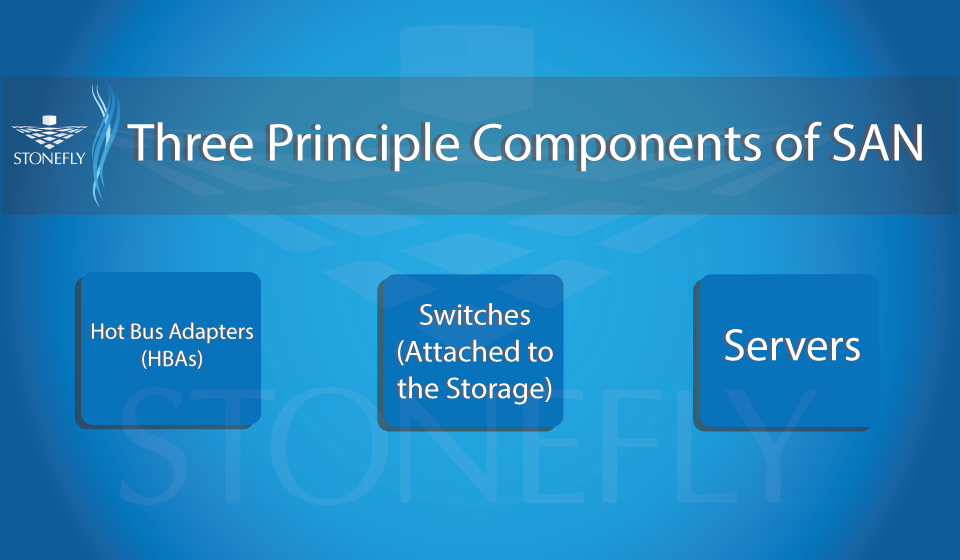
The storage system and the switches are interconnected and the physical interconnections must support the bandwidth. These components handle peak data activities.
Why is SAN used?
There are numerous reasons to use SAN; here are some of them:
- SAN is used to enhance the availability of applications if you have multiple data paths.
- To remediate the performance of the application, if you face off-load storage functions
- In order to increase storage utilization and effectiveness, as SAN provides tiered data storage.
- To revise data protection and security.
SAN (Storage Area Network) is a network designed to handle large data transfers. Using high end servers, multiple disk arrays and interconnected technology, SAN supports replication on business networks.
SAN also plays an important role in an organization’s Business Continuity Management (BCM) activities.
StoneFly’s SAN Appliances:
The SAN appliances at StoneFly come in single node and high-availability node configurations. High availability node is a full active-active cluster. It has two active-active head controllers plus dual active-active RAID controllers.
The High-Availability SAN cluster provides a wide range of virtual server environments which include the VMware, Citrix XenServer, and Microsoft Hyper-V. The SAN cluster appliances feature StoneFusion 8.0 operating system which supports NAS and fibre channel SAN volumes. StoneFusion also provides block level provisioning and centralized storage management. It includes features of asynchronous replication, campus mirroring, snapshots per subsystem, thin provisioning, Fibre Channel SAN target, NAS (support for NFS and CIFS protocols), block level volume encryption, and optimized data deduplication technologies for increased storage efficiency.