Cloud storage is a model of data storage in which the digital data is stored in logical pools. The physical storage spans multiple servers (and often locations), and the physical environment is typically owned and managed by a hosting company.
Containerization and the Virtual Machine Environment
VMs operating systems and their applications share hardware resources from a single host server or a pool of host servers. While virtual containers’ operating systems are virtualized and workloads share operating system resources such as libraries so there is a less of a need to reproduce the operating system code.
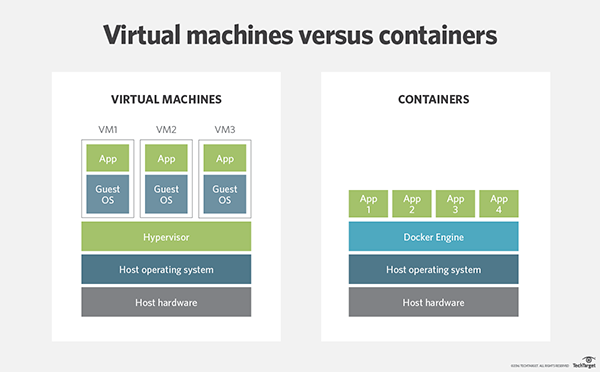
In a VM environment hardware is virtualized and each workload needs an underlying operating system. But in a virtual container environment, server can run multiple workloads with a single installation.
An organization’s operating system footprint needs to be looked at to determine if VMs or containers make the most sense. The larger the operating system footprint, the more containers may benefit an environment. Additionally, containers provide numerous benefits to organizations, including:
- Reducing the IT team resources needed for management.
- Minimizing the size of snapshots.
- Speed up the spin up time for applications with less of a need to initiate new operating system each time.
- Simplify or reduce security updates to the operating system themselves.
- Less code to transfer, migrate or upload workloads.
Outside of cost factors, VMs are beneficial for applications that require all operating system resources and functionality. Moreover, VMs have better established management and security tools. However, with the rapid use of containerization, the security aspect of it is still a discussion point on both sides of the coin.
The bottom line in choosing either VMs or containers lies upon certain aspects.
– Ask yourself, do you need to run multiple applications and servers or have a wide variety of operating systems? If yes, VMs make more sense.
– If you need to maximize the number of applications running on a minimal number of servers then you will probably want to use containers.
The reality, however, for most of the organizations out there remains the same, the ideal setup will typically contain both.