There are two concepts that pertain to disaster recovery. As you start developing a disaster recovery solution, you need to keep in mind how it impacts your organization and the cost of your disaster recovery solution. Those concepts are RTO which stands for “Recovery Time Objective” an RPO which stands for “Recovery Point Objective”.
Recovery Time Objective
To further define those, it’s probably best to draw a timeline. The middle of timeline will be the zero hour. It’s when an event happens. Maybe lightning strikes, pipes bursting or the building burning down.
As time moves forward from the event that is a measure of recovery time objective. Let’s say that your Disaster Recovery in the Cloud plan can recover your data in 12 hours. It takes you 12 hours for your users to be back online and connected to the data that was lost in the event. Then your RTO for your Disaster Recovery in the cloud plan is 12 hours.
Recovery Point Objective
That might be 24 hours for your plan, 6 hours for your plan. However long it takes you to get users connected back to the data is a measurement called RTO. Then you go backwards in time from zero event, and the longer you go from zero event is your RPO, Recovery Point Objective.
It is a measurement has to help fresh or stale the data when you do recover it. Most companies back up their data once an evening. Usually they wait till the users go home and everybody’s offline.
Let’s say 8pm is when the last backup or copy was performed. That zero hour was 8am the next morning. Then you’re RPO was 12 hours also. But it was a good 12 hours because probably very little new data came in or was changed in that time. Just the email from the people who were up late the night before.
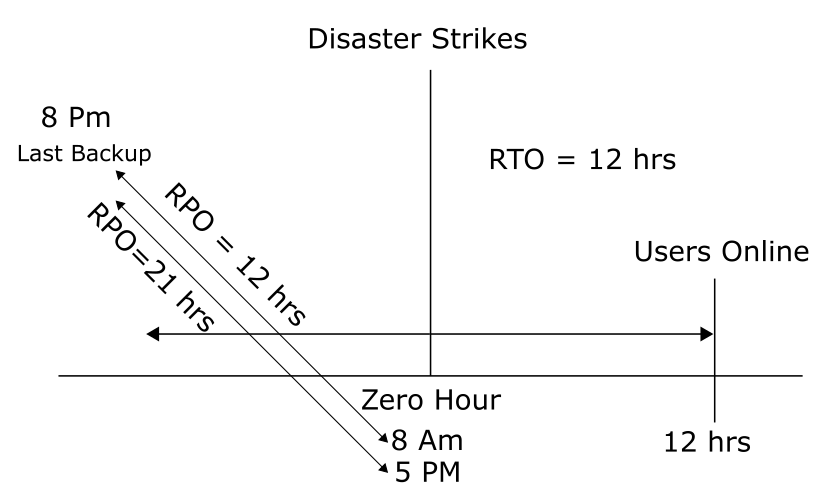
Let’s say that the zero hour is 5pm the next day. That’s a little worse, because you had a whole 8am to 5pm most likely of people going in and changing data, new data arriving, email in and out. That’s a little different, that’s 21 hours and a lot of data changed.
That’s a much bigger impact to the organization and more data that have to be recreated or you’re just going to have to not ever get back. That’s got a bigger impact to the organization.
From an RPO perspective, you try to define what is the most data we could lose, because you can’t always trust that the failure is going to happen in the morning before the next workday starts.
You could have a disaster all the way up till 7:59 till we get another backup at 8pm that next night. So your exposure is 23 hours and 59 minutes for an RPO that does a once a night backup. The impact of this as you start planning for your backup strategy and your Business Continuity Plan, it’s really all about money.
How much money am I losing when my users are not working and connected to the data they need to do their jobs, just as much as you have the impact you think of the impact of how much data dip could we possibly lose in this scenario. Disaster recovery planning is all about trying to have the lowest cost solution and the least amount of impact cost wise to the organization for that data being offline.